In a recent WVD deployment we had a requirements on blocking installation of some apps (ex. Firefox, chrome etc.) which typically doesn’t require admin rights and user can install on their profile .So we can achieve this using AppLocker which is an inbuilt feature in windows 10
Basically it allows administrators to control which files(.exe, msi, scripts) are denied or allowed to execute.
Applying AppLocker policy should be planned carefully else you will end up in blocking many things which could be required for users.
To avoid any issue related to blocking etc. on AppLocker please follow the below approach
If you planning to apply AppLocker then Install all the required apps on Base/Golder image and follow the below steps
Login to the base image and open GPO editor (gpedit.msc) and browse to Computer Configuration-Windows Settings-Security Settings-Application Control Policies-AppLocker
delete default rules as highlighted from 3 highlighted Rules

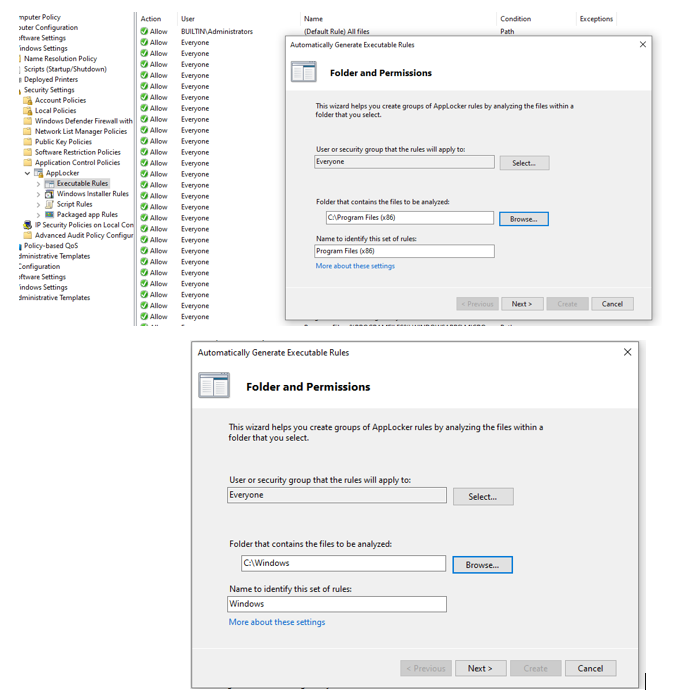
On each Rules, right click and create Automatically generate Rules..

Select the path where we usually install applications ( Program file, Program Files(x86),Windows folder (default apps ) and include if you have specified any other custom location)

When you click Next it will fetch all the installed application in that path and then click on Create

Do the same for Program Files(x86),Windows folder (default apps ) and include if you have specified any other custom location for installing apps
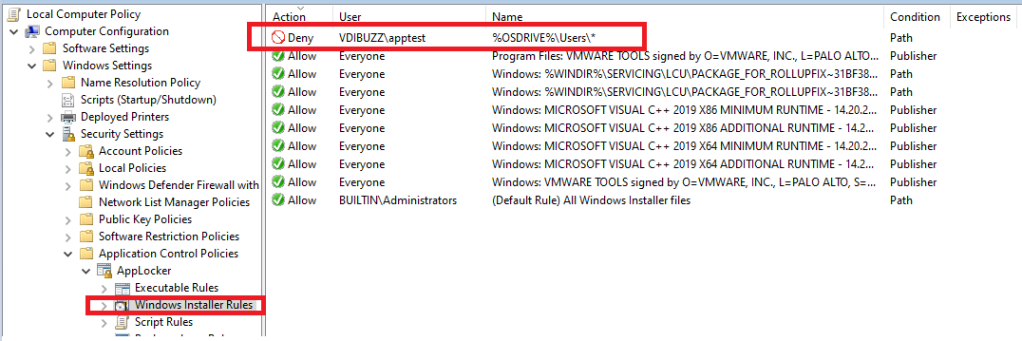
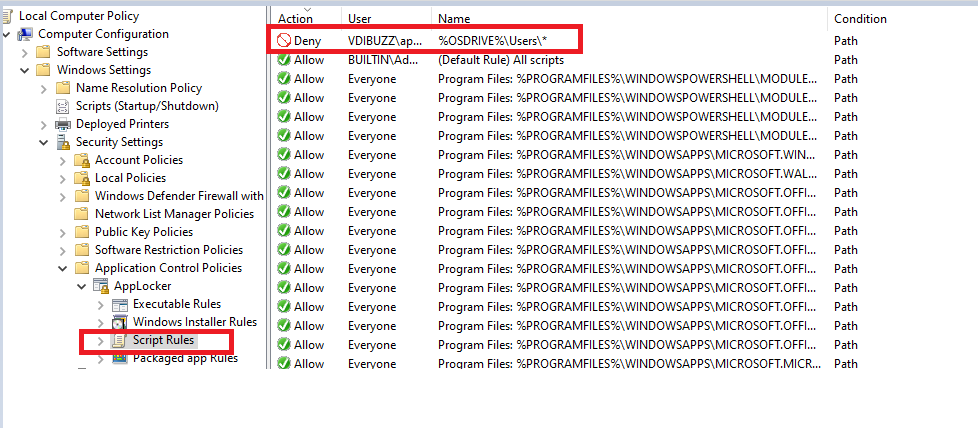
Follow the same for Windows Installer rules and Script Rules and it will look as below after autmatic rule creation


Now we have rules for the installed applications so users can only run these applications
To block users from installing any apps(.exe,.msi and script) like Firefox, chrome etc. which typically doesn’t require admin rights so on Each Rule create a new Rule and Select Deny and choose the AD group to whom you want to block

Select Path and choose %OSDRIVE%\Users\*

In this lab I am also blocking mstsc, cmd, PowerShell which normally Security people doesn’t recommend to end users to have access .

Similarly for Windows Installer Rules and Script Rules
So now we have all the requirements, lets export this settings from Golden VM and we will create GPO using this settings and apply it to Computer OU where we have our VDIs
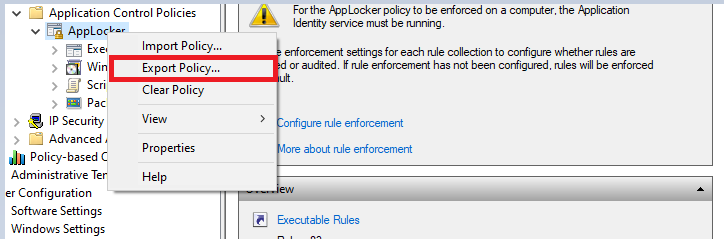

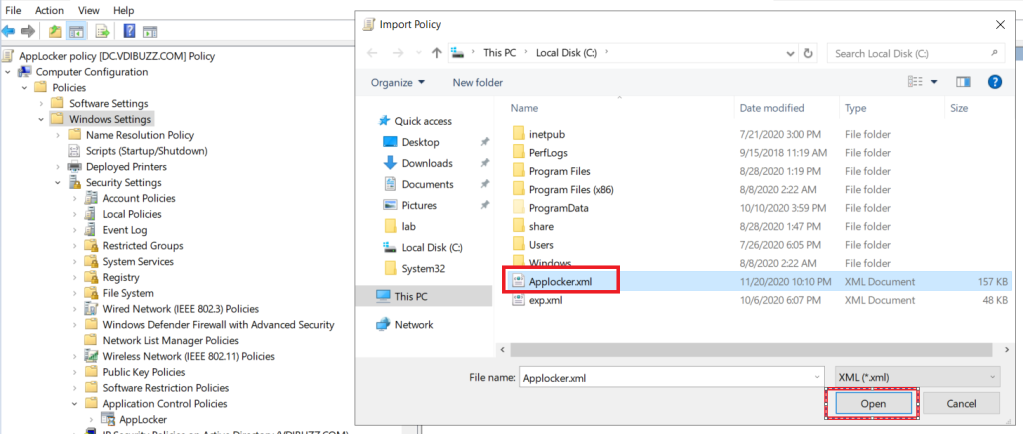
Create a GPO and import the settings from previously exported AppLocker .xml file


Once the import is complete, right click on Applocker – select Properties and check Configured under All Rules as highlighted

Link the GPO to Computer OU where we have our VDIs

Testing:
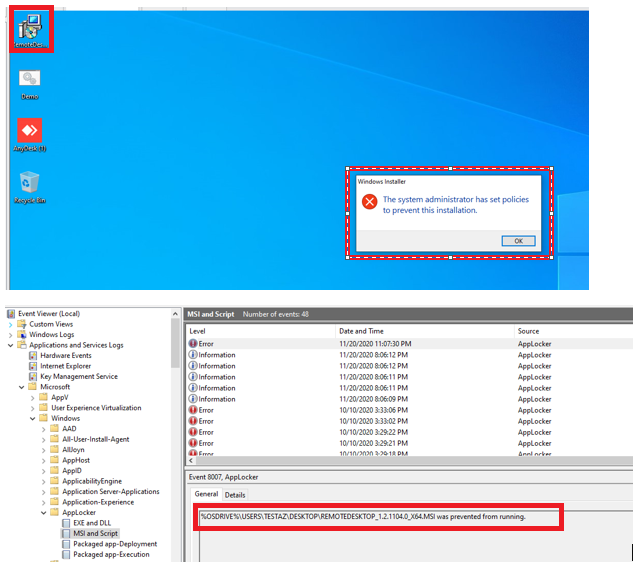
I have copied 3 types of files (.exe, msi and script ) on user desktop for testing and also we will try to launch mstsc, cmd, powershell to confirm the AppLocker behavior

When user tries to open .exe,.msi,script AppLocker will block and you can confirm this on the event log



When you try to open Notepad or any other allowed apps it will launch seamlessly



Hey there,
Major kudos for this article! 🎉 Used it to set up App Locker policies in a Windows 11 AVD Multi Session environment and it was smooth sailing… at first. I’m riding solo with an AAD Only scenario, hence no access to Group Polices. 😅
Based on the insights from this gem of a post, I harnessed the following OMA URI Settings to showcase and roll out the XML via Intune. But lo and behold, got slapped with a “not applicable”! 🤔🤷♂️
Any whizz-kids out there who can enlighten me on how to apply App Locker Policies in an AAD Only scenario without jumping into Application Control right off the bat?
Cheers and keep those geeky vibes rolling! 🚀👨💻
LikeLike
Sorry forget URL: https://techcommunity.microsoft.com/t5/intune-customer-success/support-tip-using-applocker-to-create-custom-intune-policies-for/ba-p/364981
LikeLike